This is a warning guide for Go API security.
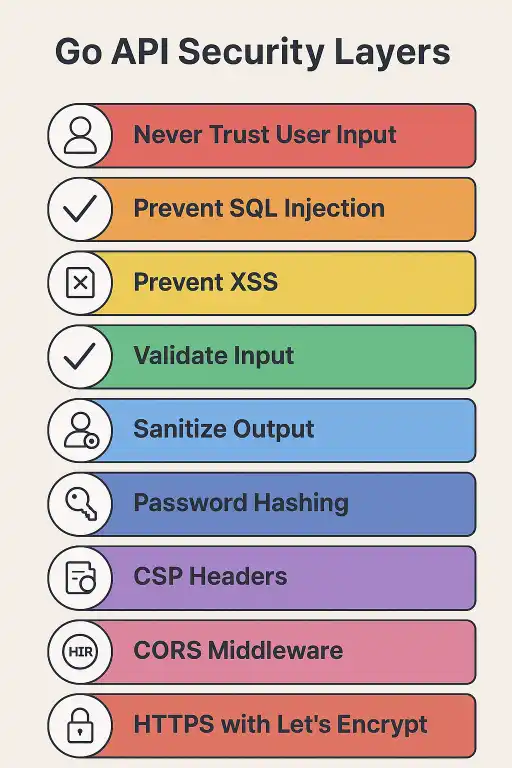
API Security Essentials
1. Never Trust User Input
- Anything the client sends = input. Query params? Input. Cookies? Input. Headers? Input. URL? Input.
- Attackers LOVE sending bad data to crash your app or steal stuff.
2. Injection Attacks
- SQL injection: Don’t do this:
db.Query("SELECT * FROM users WHERE name = '" + query + "'")
- Instead, parameterize queries or use ORMs:
db.Query("SELECT * FROM users WHERE name = ?", query)
- Same vibes for shell commands or LDAP – never blindly concat user input.
3. XSS Attacks
- If your API sends user content to a browser, it can run malicious JS.
- Use Go’s
html/templateortemplate.HTMLEscapeStringto escape output.
rw.Write([]byte("<h1>" + template.HTMLEscapeString(query) + "</h1>"))
4. Data Validation
- Go types save you from some mistakes, but semantic validation is still needed.
- Check emails, age ranges, username lengths, etc.
- Use libraries like
validatorto make it neat.
5. Sanitization
- Don’t send sensitive info like passwords in responses:
type User struct {
Username string `json:"username"`
Email string `json:"email"`
Password string `json:"-"`
}
- Optionally, use separate structs or sanitize functions for output.
6. Password Handling
- Hash passwords, don’t store them plain-text.
- Use bcrypt (auto-salts and configurable cost factor).
bytes, _ := bcrypt.GenerateFromPassword([]byte(password), 14)
- Check passwords safely:
bcrypt.CompareHashAndPassword([]byte(hash), []byte(password))
7. HTTP Security Features
- CSP: control what scripts/resources can run in the browser.
- CORS: control which domains can access your API. Browsers enforce it.
- Content-Type: always set it to prevent browser guessing.
application/jsonFTW.
8. HTTPS with TLS
- Encrypt traffic with TLS (HTTPS).
- Let’s Encrypt = free, automated certs. Go’s
autocertpackage makes it smooth.
certManager := autocert.Manager{...}
server := &http.Server{TLSConfig: certManager.TLSConfig()}
9. Integration in API
- Wrap handlers with CORS middleware.
- Validate + sanitize incoming data.
- Hash passwords before storing.
- Serve via HTTPS if possible.
Bottom line:
If you implement validation, sanitization, password hashing, CORS, CSP, HTTPS, you’ve got the foundation of a secure Go API. The next step is performance, but your app is safe AF for dev & production.
- Make Your Pets Famous Codes (August 29, 2025)
- SpiderMan Simulator Codes (August 29, 2025)
- Hunty Zombies Codes (Updated August 29, 2025)
- Hunty Zombies Codes (August 24, 2025)
- Volleyball Legends Codes (August 24, 2025)
- Anime Evolution – New All Codes (August 20, 2025)
- Restaurant Tycoon 3 – New All Codes (August 20, 2025)